New Intune Feature - Multiple Admin Approval Process
A new feature update was released in the 2211 November update for Intune. The feature is called, Multiple Admin Approval Process (MAA). The premise for the new feature is to protect against a possible compromised administrative account using something called Intune access policies. These access policies require that a change be approved by a second administrative account before being applied. An access policy states what resource will be protected and which group of accounts are permitted to approve the changes to those resources.
Currently, MAA is supported for the following resources
- Apps deployments
- Script deployments to devices running Windows of macOS
Anytime any admin goes to create or edit an object that involves a resource that is protected by an access policy, it must be approved by an approver without exception.
Let’s use a scenario to demonstrate how MAA works. First let’s create an access policy. To create an access policy, you must be assigned one of the following roles:
- Intune Service Administrator
- Azure Global Administrator
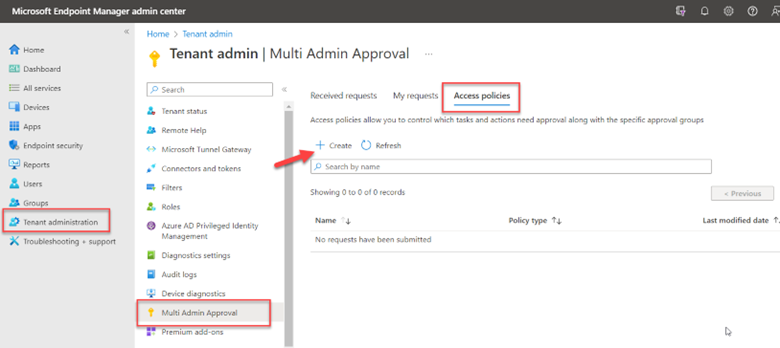
In the Microsoft Endpoint Management admin center, go to Tenant Administration > Multi Admin Approval > Access policies and click “Create” as shown in the screenshot below.
Name the policy and then choose the resource you want to protect.
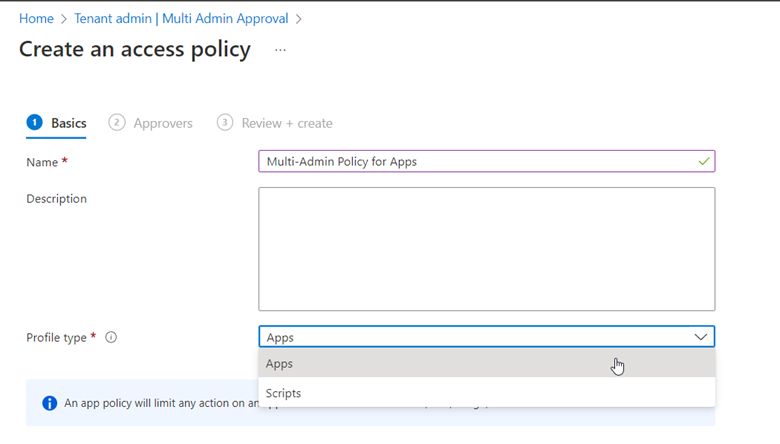
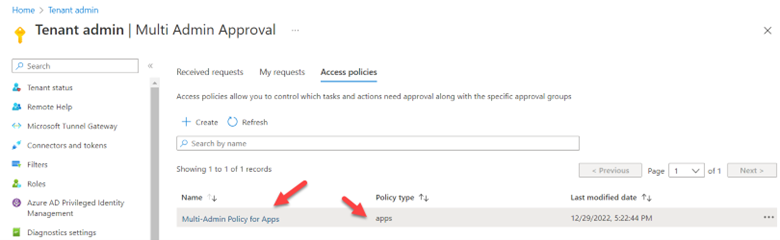
The final step is to choose an Approver group. Any user that is a member of this group can approve requests. Now I have created my first MAA access policy as shown below.
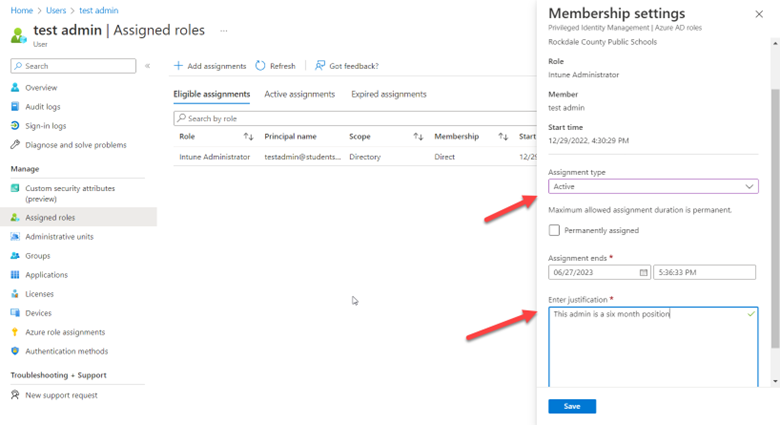
For this demonstration, I created a temporary Intune administrator account. When creating temporary accounts for testing purposes, it is good to define an active time window for these accounts so that they are deactivated automatically if forgotten. As shown in the example below, I created an account called testadmin and I defined a start and ending time for its active state.
Now, I will log on to Intune using the account I just created. I go to Apps > All apps and click Add. I then create a policy to deploy Windows 365 apps to Windows machines. In the final Review + Create screen of the wizard, there is a Business Justification section at the bottom, prompting the requester to state the justification for doing this. Also note the outlined banner alerting requester that they must enter a business justification and that the request must be approved before being implemented. Once the business justification has been entered, click “Submit for approval” and the request is now sent to Received requests where it can be reviewed.
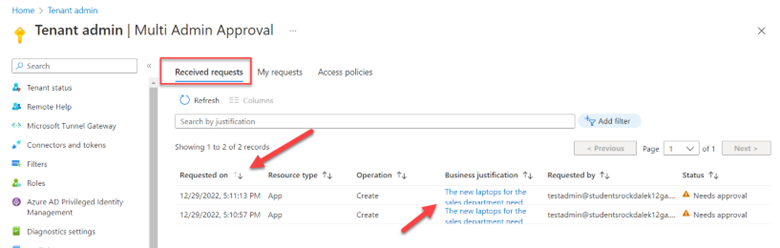
In a separate session, I have logged into Intune using an account that is a member of the approver group. As shown in the screenshot below, the request now appears (in this example, I created two requests). To approve or deny the request, click the URL in the Business justification column.
After clicking on the URL, the approver is shown the requested resource changes. The request can be approved or denied and the approver can add notes for feedback as shown in the screenshot below. 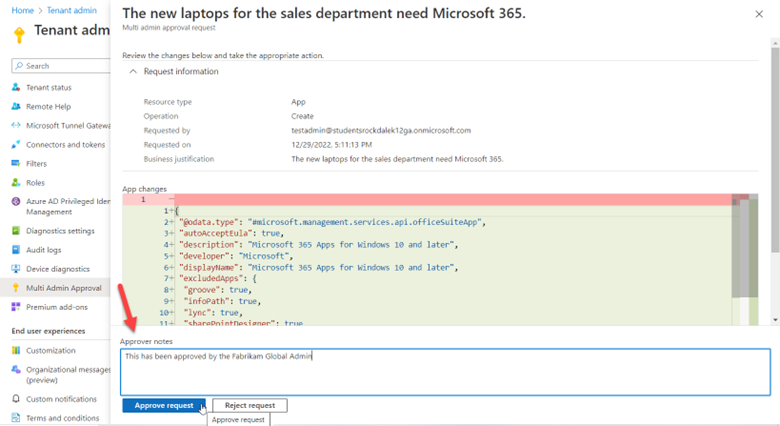
Switching back to the testadmin account, I can see the status of the requests made by that account. As shown below, one is approved while one still waits approval.
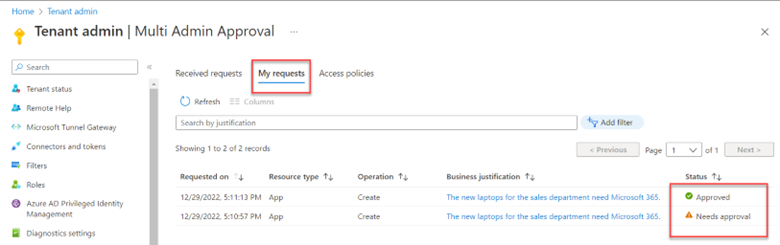
Note that any individual who submits a request and is also a member of the approval group can see their own requests, however, they cannot approve their own requests. Should no action be taken on a request for 30 days, it becomes expired and must be resubmitted.




Comments (0)