Issue#28
- Policy or Preference: Who wins the smackdown?
- Announcing: Downloadable eChapters of Jeremy's two new upcoming books!
- Kansas City Class: ON! Will you be there?
Welcome to Newsletter #28.
One of the questions I get all the time is: "Which one 'wins' if a Policy and a Preference overlap?"
Think you know the answer? I thought I did too; so let's see how that shakes out. Next,
I'm happy to announce my two new upcoming books on Group Policy.
- Group Policy Fundamentals, Security, and Troubleshooting
- Creating the Secure Managed Desktop: Group Policy, SoftGrid, and Microsoft Deployment and Management Tools
Right now, you can zip on over to www.GPanswers.com/books and learn about them, or a little later in the newsletter I'll give you the full rundown of the two books, what's new, and tell you why I had to expand it into two books!
I'm also super excited to announce our new Partner/Affiliate. Sign up, and everyone you recommend for a GPanswers.com training (or newsletter signup) means some extra dough in your pocket. More, later in the newsletter.
This Month's Newsletter Sponsored by: NetIQ
Are you stepping on other administrator's toes when managing Group Policy? It happens a lot, but there are some strategies to help you address that. In this new whitepaper, "Group Policy Management Challenges" authored by Group Policy guru Jeremy Moskowitz and NetIQ you'll learn some immediate techniques to get working better today.
Getting Down to Business: Policy vs. Preferences
Microsoft has a Group Policy blog entry called "GP Policy vs. Preference vs. GP preferences" which you should all stop and read right now. Really. I'll wait. I know you'll come back, because there's a lot more to learn on this subject. Check it out here. http://tinyurl.com/339wgx
And while I really dug that blog entry, and it was really well written and smart, there are some other angles to that Policy vs. Preferences story. And that's what I want to cover here.
How, exactly does the Group Policy engine deal with overlaps between policies and preferences? Well, theres the short answer, the middle-length answer, and the long answer. Lets go over all of them. (Were old friends nowyou knew I would anyway, right?)
The Short Answer: Policy Wins over Preferences
The short answer is that if theres a conflict between a policy setting and a preference setting, the policy setting will win. (So, for instance, items in Computer and User Configuration | Policies should always win over Computer or User Configuration | Preferences.)
Why?
Because only policies actually lock out the user interface of the application they manage (Explorer, Office 2003, etc.).
Preferences don't.
Remember, preferences are suggestions that you can give to the users application, but the user can usually just wipe them out if they want. (Although, GPPEs will re-apply again at policy refresh time by default.)
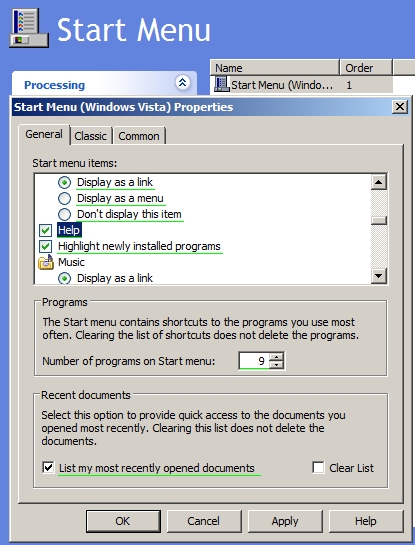
Here's a quick example to prove the point. In the example in Figure 1, Im clicking Help to ensure that the Help menu is on the Start Menu for all Windows Vista machines using GPPEs. True, this is the default anyway, but by selecting it here, Im laying down a preference that is always put on the machine.
Figure 1
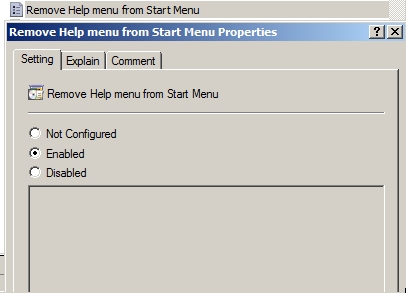
 However, if I use the policy setting User Configuration | Policies | Administrative Templates | Start Menu and Taskbar | Remove Help menu from Start Menu, as seen in Figure 2, the Help option disappears in the Windows Vista Start Menu.
However, if I use the policy setting User Configuration | Policies | Administrative Templates | Start Menu and Taskbar | Remove Help menu from Start Menu, as seen in Figure 2, the Help option disappears in the Windows Vista Start Menu.
Figure 2
 But the general case here is that policies always beat preferences. Rock always beats scissors. Or does it? Can the rock crumble when its hit by the scissors? Lets continue onward to see at least one interesting case where it doesnt work that way.
But the general case here is that policies always beat preferences. Rock always beats scissors. Or does it? Can the rock crumble when its hit by the scissors? Lets continue onward to see at least one interesting case where it doesnt work that way.
The Middle-Length Answer: Sometimes Preferences Win over Policy
You need to be careful to assume that policy always wins over preference. In fact, thats not always true. Heres an example we can use to prove it:
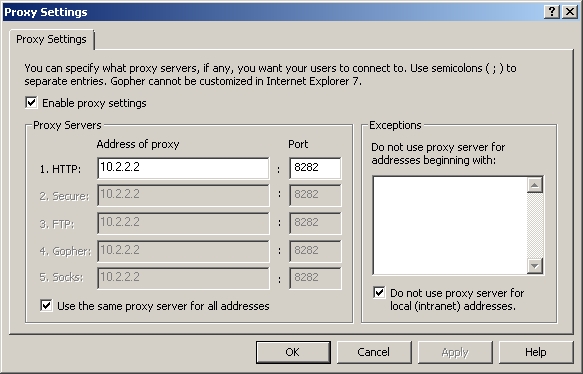
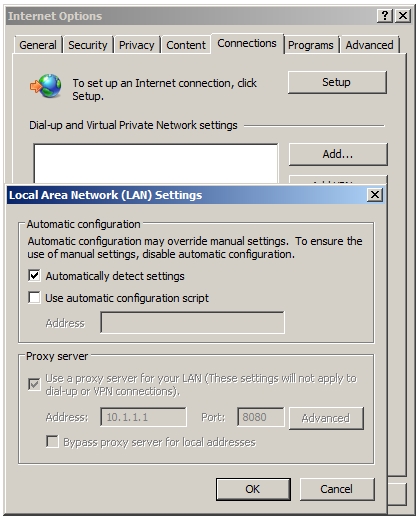
- Create a single GPO and link it to a Windows Vista or Windows Server 2008 machine that uses the Internet Settings preference extension to set the Internet Explorer 7 proxy server to 10.1.1.1 with port 8080. You can see a shot of this in
Figure 3

- Then, use Group Policys Internet Explorer Maintenance to set the proxy to 10.2.2.2 with a port of 8282. You can see a shot of this in
Figure 4
 Click on image for larger view
Click on image for larger view - Then, refresh your client via GPupdate and fire up Internet Explorer 7.
Uh oh. This seems to break the laws of nature! How can preferences win over policy? Because Internet Explorer Maintenance policy isnt really policy. Indeed, by setting the IE Home page using Internet Explorer Maintenance, the value goes to HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings in a value called ProxyServer, as seen in Figure 5. And since this is not a place for a true policy, it must actually be a preference.
Figure 5
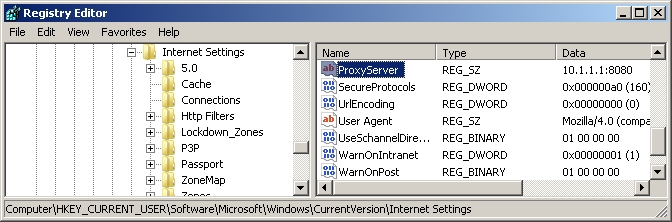 Click on image for larger view
Click on image for larger view
Indeed, the value thats being set is exactly the same for both the IE Group Policy Preference and Internet Explorer Maintenance.
Why does one win over the other? Ill show you the nuances of why in the next section.
But for now, it turns out there is a clever way to attain our goal; which is to force an IE proxy server and lock it down so users cannot change it.
Check out an obscure Administrative Templates policy setting named Disable changing proxy settings (located in User Configuration | Policies | Administrative Templates | Windows Components | Internet Explorer). A-ha! Thats true policy, so hopefully that will perform some kind of lockdown, as shown in Figure 6!
Figure 6
 But why then does that Administrative Templates setting named Disable changing proxy server settings work in a way the other guys dont? Because IE 7.0 (and 6.0 and 5.0) are all coded to look in the proper policies keys. And if theres a value there that IE recognizes, then IE makes sure to honor that.
But why then does that Administrative Templates setting named Disable changing proxy server settings work in a way the other guys dont? Because IE 7.0 (and 6.0 and 5.0) are all coded to look in the proper policies keys. And if theres a value there that IE recognizes, then IE makes sure to honor that.
And it does.
The end result is that true policy wins. You can see this in Figure 7 where the proxy server entrys values are taken from the preferences, but its locked down via the policy.
Figure 7
 For most people, the medium-length answer will be good-enough. But youre not most people. Youre looking for the most detailed knowledge you can get. So if youre curious to know why the Internet Explorer GPPE won against the Internet Explorer Maintenance Group Policy settings, read on for The Longer Answer.
For most people, the medium-length answer will be good-enough. But youre not most people. Youre looking for the most detailed knowledge you can get. So if youre curious to know why the Internet Explorer GPPE won against the Internet Explorer Maintenance Group Policy settings, read on for The Longer Answer.
The Longer Answer: Understanding CSE Timing and Overlap
To get to the bottom of this mystery, we need to understand when Group Policy applies. Recall that the Group Policy system is a last-written-wins technology. So, if you have an overlap between, say, the domain level and the OU level, the default is that the OU level will win because it was written last.
But now things become markedly more confusing. Not only is there overlap between Active Directory levels (site, domain, OU) for some of the features above, theres overlap at the feature level, where two or three CSEs compete to write their data last.
Ow.
There is some order in this chaos. But to understand it youll need an intimate understanding of what happens when the CSEs process (in the foreground and in the background). In short, the CSEs process in the order seen in Figure 8. This is a script you can download from http://tinyurl.com/23xfz3 called FindGPOsByPolicyExtension.wsf.
This exposes the same information as if you went to the following Registry key on a machine with the GPPE extensions loaded: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\GPExtensions.
There, youll see the registrations for all CSEs. The GUID of each CSE dictates the order in which things will process. Theyll process alphabetically, by GUID. So, Wireless Group Policy fires off first (thats a classic Group Policy setting), then Group Policy Environment (thats a new GPPE CSE), then Group Policy Local Users and Groups (another new GPPE CSE), then Folder Redirection (a classic Group Policy CSE), and so on.
Figure 8
So on the surface, it appears that if you had a conflict with both classic Group Policy settings and newer GPPE settings, you could just see which one ran last and bank on that setting always winning.
But thats only true if the two CSEs end up writing to the exact same places. While this is precisely what we encountered with the Internet Proxy server setting, usually two technologies dont write to exactly the same place. The tie will be broken when an application is coded to look in the proper policies keys. And, if theres a policy setting in those keys, the target application will honor the policy, not the preference.
In our mystery, its now easy to understand why the Internet Explorer GPPEs (listed as Group Policy Internet Settings) in Figure 8 won over the IE Maintenance settings (listed as Internet Explorer Zonemapping and Internet Explorer Branding). The new Internet Explorer GPPE CSE (Group Policy Internet Settings) applies after the original Internet Explorer CSEs.
But in neither case are we actually applying policy. Were really just applying preferencesusing two different kinds of technology. We finally got it to work the way we wanted when a true policy was applied, and Internet Explorer saw the policy in the policies keys and acted accordingly.
Whew. All this stuff can give you a headache. This who will win stuff is really confusing, and I havent tested every case. Be sure to test all interactions in a test lab before you roll out settings into production.
Other Items That Can Affect Group Policy and GPPE Processing
If you download Chapter 4 of Book 1 , you will learn about various policy settings found at Computer Configuration | Policies | Administrative Templates | System | Group Policy that have the configuration option to Process Even If the Group Policy Objects Have Not Changed. (It's in the section called Using Group Policy to Affect Group Policy.)
If this option is turned on for a particular CSE, then that CSE will always try to rewrite its configuration dataupon every single refresh. Again, thats not the default for classic Group Policy, but it is an option on a CSE-by-CSE basis.
However, this same always try to rewrite configuration data mantra is held by the GPPE CSEs by default, but it can also be set such that the data is laid down once and never rewritten.
So knowing this information, you might have to do a little mental math to figure out which one is going to win if you have conflicting policies plus the wildcard settings.
The Group Policy Results reports, which is discussed in Chapter 2 of Book 1, are going to be helpful in figuring out which settings ultimately applied, but theyre not going to be helpful in your understanding of why the setting ultimately applied.
Hopefully, this newsletter helps you out. This section is lightly lifted from Chapter 10 of Book 1 where I discuss this topic in even more depth.
If you want to conquer Group Policy Preference Extensions, consider taking my Group Policy 2.0 Training at www.GPanswers.com/workshop.
OMG: Now Jeremy has Two Books on Group Policy!
I've been in deep, deep quarantine the last 9 months or so. I spent three quarters of a year to get the most awesome tips, tricks, how-tos, and deep-dive information on Group Policy to you. And it took two books to do it. So, let me explain how the two books work.
The books are Companion Books to each other. Not exactly "Volume I/Volume II." But, they do go together like peanut butter and jelly.
Lucy and Desi. Group and Policy.
You get the idea.
Start out with Book 1, which is really called Group Policy Fundamentals, Security, and Troubleshooting. You already know this book, but its been revd for 2008 with the following new superpowers:
- How to create a modern management station with RSAT and the GPMC 2.0
- GPMC 2.0 Features: Filters, Comments, and Starter GPOs
- Microsofts Advanced Group Policy Management Tool (AGPM)
- Powershell with Group Policy (ooohhhh yeahhh!)
And the crown jewels...
- The Group Policy Preference Extensions: 21 new features you positively must have
But to make room for all that stuff, I moved some Group Policy Friends of the Family from Book 1 to Book 2. Book 2 is really called
Creating the Secure Managed Desktop: Group Policy, SoftGrid, and Microsoft Deployment and Management Tools. But now Book 2 is fortified with EVEN MORE AWESOMENESS. Re-read the title of Book 2 again. Lets break it down:
The main title is:
Creating the Secure Managed Desktop
And you do that by first knowing Group Policy Fundamentals (thats Book 1). Youll take your Group Policy knowledge and put it to PRACTICAL use here in Book 2. Start out by using Microsoft new Microsoft Deployment Toolkit.
Then move on to create the managed desktop with Roaming Profiles, Offline Files, the Sync Manager and more.
Deploy software to your machines using Group Policy and Microsofts newest tool: SoftGrid. Yep, to my knowledge this is the only book that has any real, meaty SoftGrid coverage. We have three MEGA chapters on SoftGrid. Youll learn how to deploy your first servers, learn all about the architecture, and learn how to sequence applications like a pro. Truly a one-of-a-kind resource. I had help from GPanswers.com Shortstop Eric Johnson with two SoftGrid chapters. Way to hit one (well, two) out of the park!
Continue on and learn how to lock down machines. Use WSUS to protect and patch your machines (thanks to Greg Shields for that awesome chapter), use Network Access Protection (NAP) to keep unhealthy machines off the network, and learn to use Windows SteadyState to put the full smackdown on your most critical machines.
Wrap up the book with a little printer magic and finishing touches, and Im totally confident youre going to love this newest member of the Group Policy book family.
Heres the best part: you can pre-order copies at www.GPanswers.com/books. Or, better yet (and this is going to blow your mind)
you can download just specific chapters you might want, today, as eChapters
Thats right. Ive worked it out so you can buy just the chapters you need. Some people will want BOTH the eChapters and the actual books. Some may want one medium. Its up to you. Your choice.
Just head over to www.GPanswers.com/books and explore the books contents then select Download eChapters now. When you do, youll be able to select the chapters from each book. Go ahead and mix and match. Just put checkmarks next to the chapters you want to download and select Buy Selected eChapters Now as seen here. 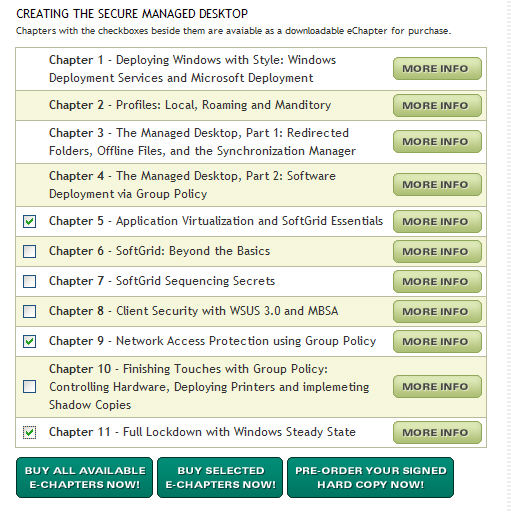 We have a FAQ on the same page you should read before you buy. But by all accounts, people are very happy with their PDF purchasing experience.
We have a FAQ on the same page you should read before you buy. But by all accounts, people are very happy with their PDF purchasing experience.
If you want signed copies, select Pre-Order Your Signed Hard Copy Now. Then once we get the books in stock, well send them to you right away.
Were expecting the first one at the end of April, and the second one at the end of May.
So, not far off. Pre-order your hard copy now and you'll be the first kid on the block when the books come in. www.GPanswers.com/books .
Let me know what you think of the chapters as you download them!
About GPanswers.com Training
I hate the word "bootcamp," but I guess that's what it is. So, if you want your butt kicked in Group Policy (in a kind, gentle way), then join me for the full week of Group Policy awesomeness:
- Two Day Essentials Group Policy Training and Workshop
- Two Day "Group Policy 2.0" Training for Vista, Server 2008 and the Group Policy Preference Extensions and
- One-Day Advanced Group Policy Training
"I finally figured out how we would block out USB ports, games and lockdown users. This alone made the entire class an extremely valuable and fun learning experience. I learned how to use Vista's event viewer to track a single event in group policy - so easy but powerful!
I learned how to set up various restrictions on a PC for different users. A tremendously valuable feature! I cannot wait to get back to the office and implement what I have learned.
I highly recommend the whole week to anyone who has anything to do with Group Policy. Nothing beats these classes, nothing." -- Mark Latham, PC Support Specialist, Mercy Regional Medical Center
Learn more about each course here:
https://www.gpanswers.com/workshop/courses/
You can take the full week, or join us for just the classes you need.
Announced Classes:
- May 5 - 9: Kansas City, MO (Lenexa, KS, really)
- Class is declared ON. If you sign up now, you'll be guaranteed a seat.
- It's the full week: Group Policy Essentials Course, Group Policy 2.0 Catch-up and Advanced One Day Course
- No other cities are announced yet. Maybe more coming soon, but I suggest if you want to get GP 2.0 with Group Policy Preferences training, then come to Kansas City!
For any public class, sign up online at: https://www.gpanswers.com/workshop/
What about OTHER CITIES in 2008?
We have a new "Suggest a city" form at https://www.gpanswers.com/suggest .
Even if you've used this before, please re-suggest your cities, as we have a new back-end tracking system. Thanks !
Private courses
I have limited dates remaining in 2008 for private classes. But call me soon, and we might be able to work it out. If you think you might want your own private in-house training (with all the personalized attention that affords), don't keep it a secret.
Call me.
If you have even a handful of in-house people interested in the training (about 68), the course pays for itself (since you don't need to ship people offsite!). I'll even travel overseas to the U.K., other parts of Europe, Japanor wherever! Have passport, will travel!
Join the thousands of administrators (and managers!) who have gotten smarter using the technology they already have.
For a public class, sign up online at: https://www.gpanswers.com/workshop/.
For a private class, just contact me at [email protected] or call me at 302-351-8408.
Become a GPanswers.com Partner/Affiliate
Amazon had a great idea. Put up some links on your web site for stuff you love, and when people buy stuff you recommend, you get some extra dough. We now have a similar program. It's super easy to sign up and get started. We provide you with your own tracking links and you get credit each time someone signs up for a class or signs up to be on our Newsletter/Tips.
It's that easy. Learn more about the program and start making some extra dough today by checking out www.GPanswers.com/partners.
Don't forget our Sponsors
I can't tell you how often I hear that people LOVE the Solutions Guide we have at GPanswers.com/solutions. Inside, you'll find both free and third-party products which extend the reach of Group Policy, or let you do something you haven't discovered before!
So, head on over to the Solutions Guide and see what other goodies are available!
Be a GPanswers.com "Booster"
Do you feel you get value out of GPanswers.com and want to see us grow? Well, I'm a Group Policy guy, not a web guy, so I need to pay for my web services somehow and enhance the site and bring you more stuff (both features and content).
If you'd like to help out, please consider making a one-time donation, or become a monthly GPanswers.com Booster for just $5 a month. If you and just 500 other people do it, I'll be able to pay for all the web bills each month and really take the site up a notch.
To help GPanswers.com and donate, here's how:
- Click here for a one-time donation (update quantity in cart)
- Click here to help with a $5 a month GPanswers.com Booster
Thank you for your support!
Subscribe, Unsubscribe, and Usage Information
If you've received this message as a forward from a friend, or are reading it online in the archives, you can sign up for your own newsletter subscription .
Also, if you want to unsubscribe, you can do that, too (but we'll be sad to see you go).
For all Subscription information, we have a one-stop-shop page at the following address: https://www.gpanswers.com/newsletter
You can use this information as you see fit, but if you're going to copy any portion, please FORWARD THE ENTIRE email.
While Moskowitz, inc. tries to ensure that all information is technically accurate, we make no warranty with regard to the information within. Please use at your own risk.
If you need personalized attention regarding subscriptions and unsubscriptions, just email me: [email protected]
Please POST your technical question on the GPanswers.com/community forum whenever possible.
If you have questions about ordering a book or signing up for a public class, contact my assistant Margot at: [email protected] . I endeavor to respond to everyone who emails.
Thanks for reading!




Comments (0)