Issue#20
Newsletter 20: Looking ahead to Vista, IE7 and other upcoming software releases In this issue:
- It's Issue 20
- Industry Update
- GPanswers.com updates
- Moskowitz, inc. Technology Takeaway (r)
- IE7 is on the horizon, how do I control my rollout?
- What do I need to know about GP in Vista?
- What about Exchange 2007, Office 2007 etc.?
- How do I know what settings are available in each OS version?
- Get a signed copy of Group Policy, Profiles and IntelliMirror
- Upcoming conferences, appearances, and classes
- Welcome new sponsors
- Free Education!
- Subscribe, unsubscribe, and usage information
This Month's Newsletter Sponsored by NetIQ
Download "Why Group Policy Matters," the informative whitepaper co-authored by Jeremy Moskowitz and NetIQ. This paper discusses the power of Microsoft's Group Policy and how organizations can better leverage the technology to address key business issues and help your organization attain its efficiency goals. Download the paper today.
GPanswers.com News
New assistant for the GPanswers.com community forum
While Ron takes a break, Adam Vero has stepped up to the plate to help keep GPanswers.com the best web resource for all things relating to Group Policy. Our thanks go to Ron for all his help in the past.
Adam has over 13 years of IT experience in a variety of fields including programming, teaching, systems management and now runs his own consultancy business, Meteor IT Ltd.
If you have not already joined in the discussions, why not come on in to the GPanswers.com forums and share your questions, answers, experiences and hot tips with other GP fanatics.
Industry News: Microsoft Buys DesktopStandard
This, my friends, is a whopper.
If you haven't read the news, do so here. Now that you've done that, what exactly does this all mean?
Well, Group Policy (the engine) has a lot of moving parts called CSEs, or Client Side Extensions. There are 18 in XP and 21 in Vista. And DesktopStandard's PolicyMaker produc adds another 21 CSEs. So, if none get "cut", eventually we'll have 42 CSEs. (I predict several will be cut, like Powermanagement, because Vista already has a similar one.)
DesktopStandard also has (had?) a product called GPOVault: This is a "Check-in / Check-out" GP management system which is built right into the GPMC. I like this tool because, well, it's just built right in to the GPMC, which means I don't have to load ANOTHER console to do the dirty work. So, the idea is the Sally creates the GPO, Fred makes sure it's Kosher and Kirk puts it in play. All around a welcome addition.
The last "big" product DesktopStandard had was PolicyMaker Software Update. Imagine WSUS that actually worked with GPOs and that understood Active Directory. And, instead of using an SMS for the "really big guys", we could just deploy patches using GPOs! Wouldn't that be a great product? Well, that's what this was. However, I'm 99% sure this product won't see the light of day at Microsoft. Microsoft already uses WSUS for the "small" customers and SMS's patching technology for the big customers. This product kind of fit in the middle, and well, I bet that's about it for this product.
In the end analysis -- it's great. More stuff for GPO admins to know and love. And more power to do what they love to do.
Stay tuned for more info as it comes up. You bet I'll be all over this when I have more to share.
Technology Takeaway (r), a Service of Moskowitz, inc.
Looking ahead to Vista, IE7 and other upcoming software releases
IE7 is now at Release Candidate 1, so it's only a matter of time...
Maybe you have already tested IE7 and are happy that it interacts with your systems properly. Or perhaps you have some intranet application that either won't accept it (some look for a user-string of IE5 or IE6 specifically so they spit it out as being unacceptable) or don't work in some way (blocked popups causing issues for example). Or maybe you just haven't had a chance to test it yet. Either way, like all good system admins, you probably want to be sure that your users can get the most out of the new features and continue to work efficiently
You can download IE7 RC1 here if you have not already done so, and take a look at the new additions such as tabbed browsing and the phishing filter that mean Microsoft is closing the feature-gap on other browsers such as Firefox and Opera. Once IE7 is finally released it will be made available via Windows Update as a high-priority update. There has been much speculation that this means a high proportion of users will get the new browser before they know what to do with it, and before system administrators have been able to thoroughly test with intranets and other internal systems. Have no fear, it's a lot more controlled than that!
For starters, if you are using SMS, WSUS or SUS to manage all of your updates anyway, then read no further, you have it all under control (although if you are still using SUS 1.0 you should be aware that support ends on December 6th so you really ought to be upgrading to WSUS fairly soon).
So, if you're not using SMS or (W)SUS, what happens? Well, if your users are not local admins, then - nothing. They don't get prompted to install the update and it won't be pushed on them or automatically installed, period. If they are local admins then they will still get a choice to install or not - and we know how good some users are at making uninformed choices. For this scenario, Microsoft have kindly provided the IE7 Blocker Toolkit which will make sure that these less-managed machines won't get the new browser through Windows Update. In a nutshell, this blocking is done by creation of a registry key. The toolkit provides a script which can be run to create or remove this, and better still an ADM template to apply this via Group Policy. Here's a quick step-by-step on how to do this:
1) Download and run the IE7 Blocker Toolkit which will prompt for a location to extract the files, including the ADM file we will need in a moment.
2) Run the GPMC and create a new policy or edit an existing one which is linked to a location containing the computers which you wish to block from receiving IE7 via Automatic Updates
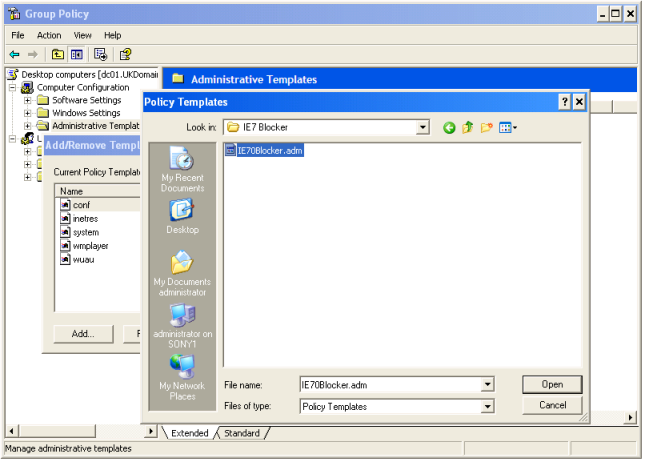
3) Navigate to Computer Configuration > Administrative Templates and right click > Add/Remove Templates. Click "Add" and Browse to where you extracted the files (see below)
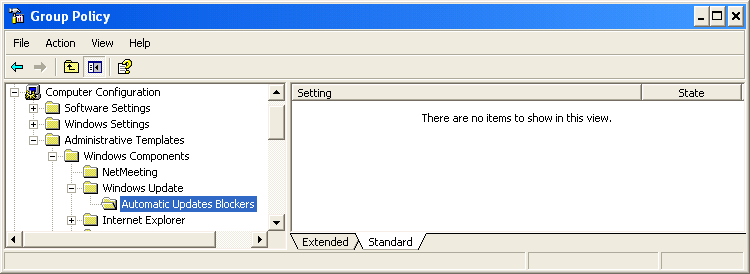
4) Now that the ADM template is added, browse down to Computer ConfigurationAdministrative TemplatesWindows ComponentsWindows UpdateAutomatic Updates Blockers. If you see "There are no items to show in this view" as shown below, then go to Step 5, otherwise skip to step 6
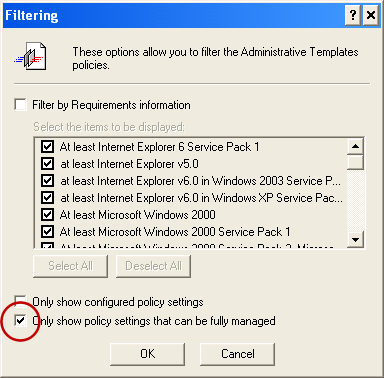
5) If you can't see the settings from the ADM file, you need to change the Filtering you have on. Go to View > Filtering and then CLEAR the box "Only show policy settings which can be fully managed" which is ticked by default as shown below.
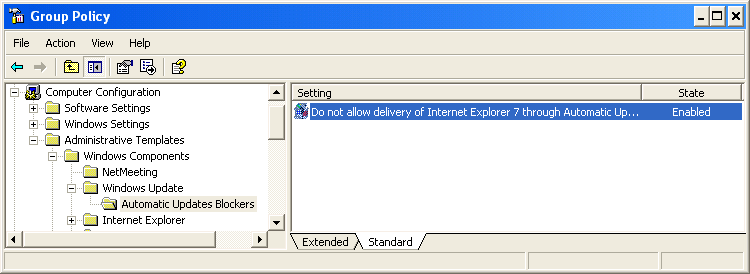
6) Now you can see the setting to block the delivery of IE7 set it to "enabled" as shown below, and users will not get prompted by Automatic Updates to install this and if they do use the "Custom" feature of Windows Update they will be prevented from installing it.
Unfortunately this won't prevent users with local admin rights from downloading and installing the browser as an MSI for themselves, but that's the reason to only let those who know what they are doing to have those admin rights in the first place, right?
What do I need to know about Group Policy in Windows Vista?
Not much has changed, really - apart from a total re-write of the format for policy templates, where and how they are stored, and a whole bunch of new settings! The two most important things to understand are that your existing policies will simply continue to work on your existing machines, and that you can only edit policies for Vista and Longhorn on a Vista or Longhorn machine.So, what is happening to ADM files? The short answer is that any custom ADM files you have will continue to work and the new GPMC will be able to use them in creating or amending policies. But the new ADMX format and syntax (which is XML-based) provides a few key benefits.
The biggest of these is that you can create a single central store for ADMX files which are used by your policies, rather than each policy storing its own copy in the GPT, which can lead to sysvol "bloat" and slow down replication between DCs. The second important point here is the separation between the ADMX file which contains settings and their effects, and an associated ADML file which contains language-specific bits which are exposed through the GUI (the description of the settings and the "Explain" tab for example). So admins can view and manipulate the same policies using a different language interface, rather than all having to share a common language which may not be native to many of them. Of course, for in-house custom files the same is true - but someone has to write the ADML files to go with the ADMX.
You have probably heard that there are all kinds of new policy settings available to manage aspects of your Vista machines. Some of the most important classes are those for Power Management, Device installation and Removeable Storage. All of these are areas you may want to control centrally to manage costs (by reducing wasted power consumption) and business risk (reducing the ability of Joe from Sales taking the whole customer database with him on a USB thumbdrive when he leaves). Printer management and IE configuration have also both been made easier with GP for Vista. There's much more information on the MS website about these new Group Policy categories.
Other things which have changed in Vista Group Policy processing include:
- the fact that the whole process now runs as an independent service
- you can have multiple Local Group Policies (yes - policy local admins differently form your normal users at last!)
- much better handling of connection status through "network location awareness" - slow link determination, or updating GP when a VPN is connected or a machine returns from hibernation for example
If you want to know more, get it straight from the horse's mouth by watching this 42-minute webcast:
Program Manager Mark Lawrence discusses the Group Policy improvements in Windows Vista
(Live ID / Passport required to register)
One last thing for this edition while we're on the subject of Vista - your WSUS server won't get updates for Vista Beta editions without being configured to do so. Recommendation from MS is to configure a separate WSUS server (which must have WSUS sp1) just for your Vista Beta machines to update from, and configure this to fetch the updates from the MS Beta Update Server
Configuration is straightforward, simply by running a VBS script which is already on the WSUS server from a command prompt:
cscript.exe "%programfiles%update servicestoolsToggleMUUrl.vbs" beta
You can revert to the normal update server by repeating this command without the 'beta' on the end, but as already mentioned, you really ought to be doing this on a dedicated box anyway, and remove / reinstall WSUS completely once your Beta phase is over. More info here.
What other GP goodies are there out now for upcoming products?
Just a couple of quickies about other upcoming bits of software which you may want to begin testing, and how this impacts on your GP world.
Firstly, Office 2007 brings with it a whole bunch of changes to the way it is deployed and of course more GP settings to control it. Significantly, to deploy from a central administrative install using GPSI you only need to point at the main MSI file and this will detect that this is being called by GP and go off to get all the MSI files it needs from the install point.
There is no longer on e single huge all-in-one "office.msi", in other words. Another big change for GP fans is that Outlook 2007 security can now be configured through regular Group Policies rather than having to configure a security template and publish this via the Exchange server. You can still do it the old way if you prefer, but for new installs a pure-GP method makes good sense. More about configuring security for Outlook 2007.
Of course, to manage Group Policy for Office 2007 you need to get the ADM files which are found in the Office 2007 Resource Kit here. (NB: this link only works if you are a registered Office 2007 Beta user, ie you installed the Beta, ran one of the apps and registered the product)
Exchange 2007 Beta can be run on 32 bit systems, although the final release code will only work on 64 bit and you won't get support if you put your production environment on the 32-bit version. However - for either platform you need to be running MMC version 3 (which we talked about in Newsletter 18) as well as .Net 2.0. Read more about MMC 3.0 here and download the version you need before you try and install the Beta. Click here to view the full system requirements for Exchange 2007 Beta 2
How do I know what settings are available in each WIndows version?
A particularly common question, along with its cousin "where do I find the setting to do 'X'?"Periodically, MS issue a complete spreadsheet of all the Group Policy settings, along with the text you see on the explain tab to help work out what it does, and a column showing what the reuirements are (in other words, which OS version and other things are needed to make the setting work). You can filter the list easily on these columns, and use the usual Find feature (CTRL-F) to search for particular text.
The latest version of the Group Policy Settings file is up to date to Vista Release Candidate 1. If you are using Vista Beta 2 some of these settings do not apply, and you should check the Vista Beta2 GP settings instead, although the file is a lot less detailed. The older file for versions of Windows up to 2003 sp1 / XP sp2 is still useful if you are not moving to Vista just yet, as it shows which ADM files you will find the settings in.
That's all the space we have for tips in this issue. please continue to submit your own tips or links to useful information in theGPanswers.com forums.
Get signed copies of...
Group Policy, Profiles and IntelliMirror for Windows 2003, Windows XP and Windows 2000 (THIRD EDITION)
-and-
Windows & Linux Integration: Hands on Solutions for a Mixed Environment
Do you have the new THIRD EDITION of the Group Policy book? It's got 50 new pages, fully covers XP/SP2 and Windows Server 2003/SP1, an armload of new tidbits here and there, and whole new section on the Security Configuration Wizard.
Order your signed copy today by clicking here.
Additionally available is my new title Windows & Linux Integration: Hands on Solutions for a Mixed Environment from www.WinLinAnswers.com/book.
Oh, and if you own either book, and want to say nice things on Amazon, please do so! That would be great. Thanks! You can do so here:
http://www.amazon.com/gp/product/0782144470 (GPO book)
http://www.amazon.com/gp/product/0782144284 (WinLin book)
Choose the right Active Directory and Group Policy Course for you
Did you know that here at GPanswers.com, we have three courses, including an ADVANCED course. (It's true!) Online, we have a new-ish "Group Policy "Rightsize" Tool" which helps you decide the best course to take for your situation. We have both PRIVATE and PUBLIC classes. Again, use the Righsize tool to get a total understanding of your options.
Upcoming Public Classes, Appearances and Conferences
Public Two-Day Workshops for the Remainder of 2006:
- Oct 12-13: Phoenix, AZ -- FULL ! (Come to Portland, Dallas or Seattle)
- Oct 23-24: Portland, OR -- 11 seats left ! (Special note: No laptop required for this course. Leave your laptop at home if you want!)
- Oct 30-31: Dallas, TX-- Lots of seats left
- Nov 21-22: Seattle, WA -- Lots of seats left
Why THESE cities? Because people used the "Suggest a city" form at https://www.gpanswers.com/suggest and ASKED me to have classes here.
Here's hoping you'll take advantage of the opportunity! Learn more and sign up at: https://www.gpanswers.com/workshop
(Don't forget to scroll all the way to the bottom of that page and locate your city!)
Or, if you think you might want your own in-house training (with all the personalized attention that affords), I'd love to join you onsite!
If you have even a handful of in-house people interested in the training, the course pays for itself (as you don't need to ship people offsite!). I'll even travel overseas to the U.K., other parts of Europe, or Japan - or wherever! Have passport, will travel!
Again, while the training course isn't officially endorsed by Microsoft, the class does have the distinction of being a suggested avenue for intense Group Policy training by members of the Group Policy, Microsoft Consulting Services, and Product Support Services teams at Microsoft!
For a public class, sign up online at: https://www.gpanswers.com/workshop/
For a private class, just contact me at [email protected] or call me at 302-351-8408.
Free Education with Moskowitz / Microsoft / Techtarget / Dell Roadshow
Jeremy Moskowitz and TechTarget + Microsoft team up to bring you a 19-city roadshow tour titled: Deployment, Managing, and Monitoring: Getting the Job Done. Here, youâll hear me talk about how to use the tools in the box to deploy your Windows XP, Windows 2003, and Vista systems, how to use Group Policy to manage your systems, and finally how to keep tabs on them with some slick free tools!
The roadshow is still rolling until November, so thereâs a good chance weâll be near you soon! Check it out and sign up here.
Upcoming Conferences
- TechMentor: Oct 9-13 in Las Vegas. I'll be speaking on Win/Lin integration topics. All sorts of other good stuff. Check it out here. Use promotion code 'moskowitz' when signing up.
- WinConnections: Nov 6-9 in Las Vegas. I'll be doing a pre-con on Group Policy, then some regular sessions on locking down computers, some awesome tips on Group Policy tools, and how to integrate Windows and Linux into Active Directory. Check it outhere.
Don't forget our Sponsors
I can't tell you how often I hear that people LOVE the Solutions Guide we have at GPanswers.com/solutions. Inside, you'll find both free and 3rd party products which extend the reach of Group Policy or let you do something you haven't discovered before!
So, head on over to the Solutions Guide and see what other goodies are available!
Subscribe, Unsubscribe, and Usage Information
If you've received this message as a forward from a friend, or are reading it online in the archives, you can sign up for your own newsletter subscription.
Also, if you want to unsubscribe, you can do that, too (but we'll be sad to see you go).
For all Subscription and Unsubscription information, we have a one-stop-shop page at the following address:https://www.gpanswers.com/newsletter
You can use this information as you see fit, but if you're going to copy any portion, please FORWARD THE ENTIRE email.
While Moskowitz, inc. tries to ensure that all information is technically accurate, we make no warranty with regard to the information within. Please use at your own risk.
If you need personalized attention regarding subscriptions and unsubscriptions, just email me: [email protected]
Please POST your technical question on the GPanswers.com/community forum whenever possible.
If you have questions about ordering a book, contact my assistantMark at: [email protected]. I endeavor to respond to everyone who emails.
Thanks for reading!




Comments (0)