Issue#19
Newsletter 19: The File Server Migration Toolkit In this issue:
- It's Issue 19
- GPanswers.com updates
- Moskowitz, inc. Technology Takeaway (r)
- "Deep Dive" into the File Server Migration Toolkit
- Get a signed copy of Group Policy, Profiles and IntelliMirror
- Upcoming conferences, appearances, and classes
- Classes and seminars
- Welcome new sponsors
- Free Education!
- Subscribe, unsubscribe, and usage information
This issue, we've got another "big article". It's about the File Server Migration Toolkit. Why should you care? How is it related to Group Policy? Ah the suspense ! So, without further ado!
This Month's Newsletter Sponsored by NetIQ
Learn how to leverage Group Policyâs capabilities to secure and manage your desktop. Moderated by Active Directory guru Jeremy Moskowitz, this information-packed Webcast will show you how business objectives can be paired with Group Policy settings for a more secure and managed environment. Sign up today for the live webcast on July 27th.
GPanswers.com News
Announcing 1-day Advanced Group Policy Course
Have you already taken the two-day or three-day workshop? Are you looking to get "more" of what you already love? Then check out our one-day Advanced Group Policy course. We cover four big topics:
- How to create a âtotally locked downâ workstation
- How to use Group Policy tools to increase your troubleshooting ability
- How to zap registry punches down to your client machines with ADM templates and tools
- How to leverage a test lab for good Group Policy deployment practices
It's a one-day hands-on course. Right now, it's only available as a private class. So, if you want me on site, you can add this on to you two or three day workshop class -- or just have me come by for the day!
New "Rightsizing Tool" for GPanswers.com Training
I'll talk about this a little later in the newsletter. But I haven't always done a good job making it easy to decide which Group Policy class is ideal for each person or organization. Now, online, I have a new âGroup Policy âRightsizeâ Toolâ which helps you decide the best course to take for your situation. Check it out here.
New "At a glance view" of newsletter archives...
People were telling me it was hard to know what was in each previous newsletter. Too much to read to find out. Well, now at www.GPanswers.com/newsletter you'll see an at-a-glance view of all our old archives. Just find the newsletter you want -- and enjoy!
In case you didn't get the memo...
Free gift to anyone who has ever taken a GPanswers two-day or three-day Group Policy workshop (where either James or I was the instructor).
It's about time I said thanks. So, thanks!
Here's the deal: the gift is free, the shipping isn't. Sorry, I'm a small business, and that's the breaks.
Shipping for your free gift is only $5, though.
And if you hate the gift, Iâll cheerfully refund your $5 and you can keep the gift. Really! (I sound like Ron Popeil, donât I?)
Here's the fine print:
- Shipping for the gift is a flat $5
- We can accept Paypal or credit card for shipping
- US residents only
- If you can remember, please specify which public class or private class you attended (location and approximate month and year).
Note, that if you like the gift, but have never taken the two-day or three-day class, you can get one for a whole $12 (including shipping). Gifts ship right away.
Technology Takeaway (r), a Service of Moskowitz, inc. -- All About the File Server Migration Toolkit
Admit it. You've got 'em. Windows NT and Windows 2000 file servers that you just can't seem to shake. You know you want to get your file servers updated to Windows 2003/SP1 or Windows 2003/R2. And, we both know why you're not there yet: users are using UNC paths to point to shares on these file servers. And you know that if you move the data from the original servers to the new servers, all those users with UNC paths pointing to those shares are going to call the help desk (then the help desk is going to hunt you down, and you'll have to go into hiding.)
Or how about this sticky Group Policy problem: you got started using Group Policy Software Installation, and serving your installations using one file server. Now you have 50 GPOs deploying applications to your Windows XP and Windows 2000 machines. But, oops! You're ready to turn off that original file server.
But you can't.
Those 50 GPOs are depending on it.
What are you going to do?
A typical environment where files and software are originally being deployed from a Windows 2000 file server and/or Windows NT files is seen below.
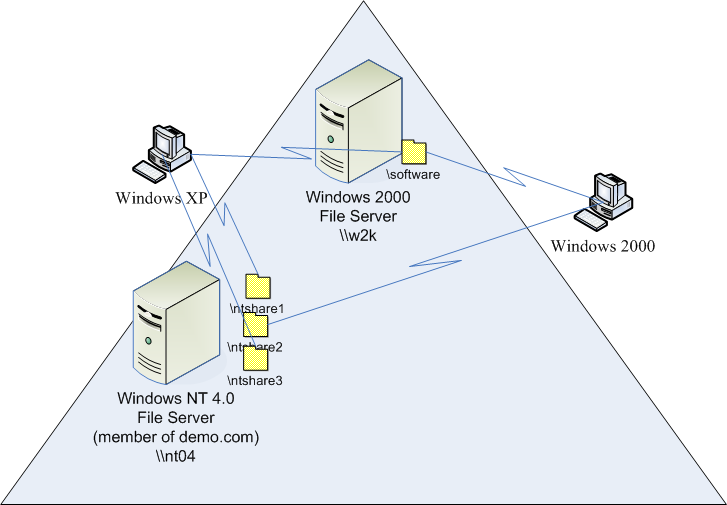
Figure 1: You're currently depending on NT 4 and Windows 2000 file servers (aren't you?)
So just turning off these servers isn't an option, and just copying the data to new shares on a new server isnât an option. So what are you going to do? The good news is that thereâs an answer [solution?] to these two tales of woe. Microsoft has a cool tool to help you take control of your old file servers and bring the data into the 21st centuryâseamlessly.
Enter the File Server Migration Toolkit . . .
The File Server Migration Toolkit, or FSMT is a free download available here. The FSMT consists of three parts:
- DFS Consolidation Root Wizard: This is another GUI tool which works some serious magic. It allows you to maintain the original UNC paths of the servers, even if youâre planning on ultimately turning those servers off.
- DFSconsolidate.exe: This is a command line tool which is called by the DFS Consolidation Wizard. While itâs possible to use this tool on its own, weâre only going to explore its use in conjunction with the DFS Consolidation Root Wizard.
- File Server Migration Wizard: This is a GUI tool which helps you plan your migration from the source servers to the target servers. Then, it actually performs the copy of the original files to the target destination. Weâll explore this a bit later.
Understanding Our Goals . . .
The first thing to know is where to start. You need to pick a source server (where the files are currently stored) and a target server (where you will migrate the files to). Letâs work through an example to help us understand where we are and where weâre going. Our Before Picture: You can see this in Figure 1. We have an NT 4.0 file server (nt04) with three shares containing user data. We have a Windows 2000 server with one share used to deploy software. Letâs take a closer look at whatâs happening in our world. Our Windows XP machine needs access to the following:
-
- nt04ntshare1
- nt04ntshare3
- w2ksoftware
Our Windows 2000 machine needs access to these servers and shares:
-
- w2ksoftware
- nt04ntshare2
Now, letâs introduce our target file server, fileserver6, whose job it will be to receive these shares and requests.
Our After Picture: The goal is to consolidate these existing shares onto fileserver6 and turn off the Windows 2000 and NT 4 servers. We need to perform this task in a way which preserves the original paths of each of the aforementioned shares. Yes, you read that right. We want to be able to access the data thatâs currently on the computers weâre turning off as if they were still turned on. Oh, and of course, you want to make sure security is preserved all along the way.

Figure 2: Our goal is to turn off the NT 4
and Windows 2000 file servers but allow access to all data using the original server names (even though those computers are off
Here, in Figure 3 we can see our Windows XP machine accessing a directory of files on both nt04ntshare1 and nt04ntshare3 shares. The goal is for this Windows XP machine to continue to perform the same commands, using the same UNC paths after we move the files and turn the original file servers off.

Figure 3: Here, our Windowx XP machine is viewing files via UNC paths
To get to our promised land, we'll leverage a part of Windows that has been around for a while, but still isn't in widespread use: the Distributed File System, or DFS. DFS's goal is to accept incoming connections and route them to existing shares (this is sometimes called referrals). You might say it's like a "share of other shares" because it allows you to basically "hang" existing shares off a new DFS share, or, more technically the "DFS root". There are two kinds of DFS roots: standard and domain-based (sometimes called an Enterprise root). Standard roots only live on one server. Enterprise roots live at the domain level, which means that they're fault tolerant. If one server that's part of the DFS referrals goes down-no problem-referrals just keep on truckin'. Learn more about DFS (which is substantially different in Windows Server 2003 than in Windows Server 2003 / R2) by reading more at the following link.
Here's the roadmap to get to your destination:
- You'll determine where you want to stash your new files. In our example we're going to be using fileserver6.demo.com.
- You'll rename any file servers you plan on permanently retiring. Since you're retiring them anyway, it doesn't really matter much what the name becomes.
- We'll be renaming our nt04 server to nt04-ret to signify that it's retired. Same goes for w2k to w2k-ret. Then, finally, when we're all done, we'll be turning off this server permanently.
- We'll use the DFS Root Consolidation Wizard to control basically, "reroute" new incoming requests for the retiring servers (nt04 and w2k) to the new location (fileserver6). Note that I could use two separate servers in my migration example. That is, I could use one server to hold the DFS Roots and another to hold the files. However, to keep things simple, I'll use fileserver6 for both roles.
- We'll actually move the files we need from the shares on our old servers to our new location on fileserver6.
So let's do it!
Getting Started with the FSMT and DFS Consolidation Wizard
The FSMT comes as a single MSI, but, as we stated has three separate components. The File Server Migration Wizard is meant to be run directly on the target file server. However, the DFS Consolidation Root Wizard and the Dfsconsolidate.exe command-line tool can be run anywhere; you can choose to run these tools on the target server or not.
Note the FSMT documentation makes special note of MSKB article 829885 which talks about a DFS hotfix. The implication is that this hotfix must be loaded upon the target DFS server. However, this hotfix is built into the Windows Server 2003/SP1, and is not needed when the target server is Windows Server 2003/SP1 (in my case fileserver6.) However, the FSMT documentation doesn't tell you one critical step: be sure the DFS service is started and set to Automatic for future restarts.
After the FSMT is loaded, as I mentioned earlier, we must change the name of NT04 server to nt04-ret and the name of w2k to w2k-ret (or something else that's meaningful to you). The reason why we must change the name is so that when clients try to connect to nt04 or w2k neither actually exists anymore. And, we'll be able to fool those incoming requests to nt04 or w2k into shimmying over to the new place on fileserver6.
In my tests, renaming an NT4 server wasn't as easy as I would have liked. Simply renaming it doesn't magically change the name in Active Directory (like it would if I renamed a Windows Server 2003 or Windows XP machine). I had to drop the machine into a workgroup, rename the machine, and rejoin the domain (demo.com.) And, of course, along the way several reboots were required. Finally, I had to delete an orphaned computer account for NT4 using Active Directory Users and Computers. In contrast, renaming the Windows 2000 server was a snap. Just rename and reboot -- easy. No muss, no fuss.
Now that my NT4 server and Windows 2000 servers are renamed, I'm ready to run the DFS Root Consolidation Wizard. The Wizard is pretty straightforward, asking only a minimum of information:
- DFS root server: This is the location where the DFS root will be held. In DFS terms, this will be a "standard root"-which exists solely on the server you specify. Note that the root cannot be on a Domain Controller. In my example, I'm choosing to put the DFS root on the same server where the files will ultimately go-fileserver6. However, you can create the root on a server cluster if you want to increase the redundancy of the stand-alone root.
- Local path of the folder: This is the top level directory where you want to store each migrated server. If we were migrating 10 servers, you would expect 10 subdirectories underneath this top level directory containing names of each migrated server. For my examples, I'm choosing the name c:migservers
- Specify which servers to consolidate (as seen in Figure 4): Here, you'll map the original name to the current name (as seen below.). We're migrating two servers, (original name nt04, current name nt04-ret and original name w2k, current name w2k-ret) so we'll have two mappings in the list.
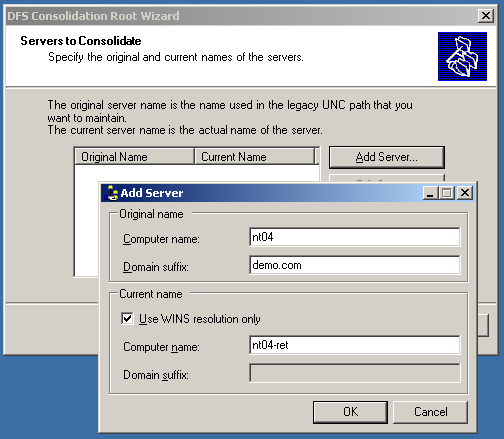
Figure 4: The "DFS Consolidation Root Wizard" helps you map renamed servers to original names
If the Wizard finishes without errors, you've completed the first big step. Now, before you do anything else - take a moment to pause and check something out: Go back to your Windows XP machine (see first figure) and run those exact same dir commands access the servers and shares nt04ntshare1 and nt04ntshare3. Without rebooting the Windows XP machine (or logging off and back on), note those same dir commands just continue to work! This is because the DFS Root Consolidation Wizard has now mapped nt04 to nt04-ret-so all the shares via UNC paths still work.
And, let's take a quick second to see what really happened in the c:migservers folder on fileserver6. Below, you can see it created two subdirectories, which are each shared, and which contain another subdirectory of each server's original share.
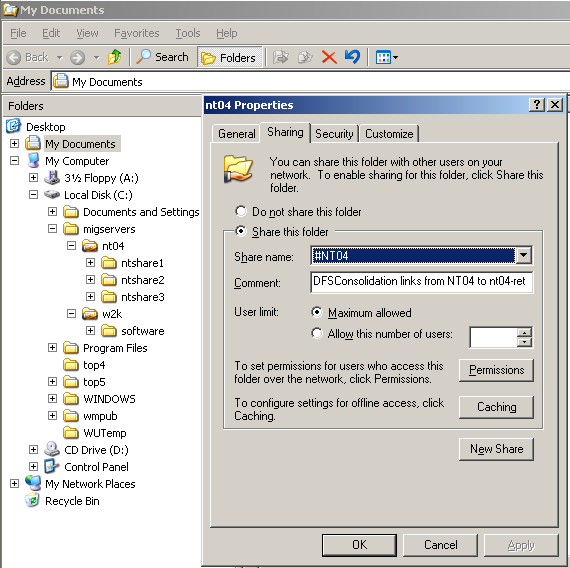
Figure 5: The DFS Consolidation Root Wizard created a new share representing the old server
However, using Explorer locally and drilling down to one of the directories, say, ntshare1, will get you an error. This is because a DFS link only points to the right (new) location when using a remote referral (not a local one). Also note that each server is now represented by a share, #servername, such as #NT04, seen above. This was created by the DFS Consolidation Wizard.
It is possible to use the DFS Consolidation Wizard if your shares are on Domain Controllers. However, the same rule applies for Domain Controllers as for regular file servers. That is, the server (Domain Controller) must also be renamed. And unfortunately this can be a pain in the neck. Microsoft does have some Domain Controller renaming guidance:
- For NT 4.0 Domain Controllers, see MSKB 150298
- For Windows 2000 Domain Controllers, see MSKB 296592
- And, even though it's easier still with Windows Server 2003, there's some guidance at MSKB 325354.
There is one piece of magic that the DFS Consolidation Wizard cannot directly help with, and that is if you already have hard coded, persistent mappings. Meaning that if someone has used the /persistent flag while using the net use command to map a drive letter (or the corresponding Explorer commands) those mappings will now fail. But if you're using log in scripts to map the drive letters each and every time a user logs in-no problem! This is because every time a request goes to the old server name, a new lookup to the DFS is generated and routed appropriately.
Actually Migrating the files
To actually migrate the files, you create a project contained within the File Server Migration Wizard (FSMW), which appears as an icon on the start menu. The beginning steps are rather straightforward: create a new project, point the File Server Migration Wizard toward the new DFS consolidation point you created earlier (fileserver6), and watch it recognize the servers, as seen in Figure 6.
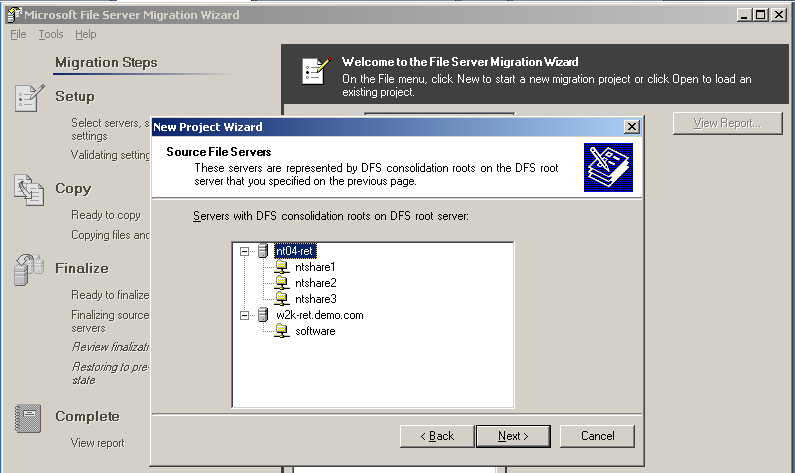
Figure 6: The File Migration Wizard should recognize your servers after you consolidate them using the DFS Consolidation Wizard
Then, you can tell the FSMW which directory you want to plunk the new files in. I chose a new directory on fileserver6 called c:migfiles.
A quick note on what is and is not copied. Of course the files themselves are copied. But the FSMW also copies both NTFS and shared folder permissions. What aren't copied are references to local groups. If local groups have permissions on the source's shared folders, you can use the Resource Kit tool SubInACL.exe to adjust the permissions before or after the migration to replace the local groups, or you can use a local group migration tool like the Active Directory Migration Tool (located here ).
When the project is formed, you then have the ability to make any micro-adjustments you might need (as seen in the circled area on the right of Figure 7). For instance, you might want to put the contents of ntshare1 in a directory named "Sales stuff" instead of ntshare1. This might boggle the minds of your users, but you may have a valid reason.

Figure 7: You can change settings for each share if desired, then click Continue to step through the rest of the Migration.
Finally, you can just step through the rest of the process by clicking on the Continue button, circled above at the bottom of Figure 7. The process is painless, but could take a (long) while depending on just how many servers you are consolidating. For lots and lots of servers, consider breaking up the effort into multiple "projects" to allow for some settling-in time and attention to errors. If there are errors during the copying you'll have the ability to fix the errors and retry. A nice touch is that the target servers are still available during the copying phase. In other words, there's no server downtime from the copying of files from the source server to the target server. Additionally, because it's possible to repeat this phase multiple times to fix errors, another nice touch is that only failed copy attempts are retried. You don't need to copy the whole universe again if you've already copied 90% of it.
The last phase is called Finalize. This phase should really only be done when users won't be accessing the servers. That's because in this phase, you'll disable any original access to the source shares and close any open connections. Additionally, all other project settings are locked.
At this point, you're ready for your final test. Unplug the network connections from the original servers. Then, like we did with our Windows XP machine, make sure you can get to the copied servers using the original UNC path names.
Once you're satisfied that you can get to the copied data using the original UNC paths, you can turn off your old servers, recycle them, reformat them and redeploy them for another purpose, or make a fish tank out of them (or any another arts and crafts project you'd like).
The Future of the File Server Migration TOOLKIT?
The FMST is a great tool which gets the job done. However, there are some small nitpicky points that Iâd love to see addressed going forward.
As stated, the FSMT uses whatâs called âstand-aloneâ DFS roots to do the job. In other words, it puts the DFS root on one specific server. Sure, in my example, I used fileserver6 for both the storage of the standalone DFS root as well as the ultimate storage point for my migrated files. However, I could have also split the duty between file servers. That is, one server could house the DFS root, and another server could have held the data. So, what would happen today if that server holding the DFS root went offline? That would be a major problem, because there would be no way to route to the new file server(s). The ideal solution would be to use the more powerful domain-based roots which are fault-tolerant. Then if the one server holding the DFS roots should fail, the fault-tolerant nature of domain-based DFS would kick in. Today, FSMW doesnât use domain-based, fault-tolerant roots, but I really wish it did. Again, as I mentioned earlier, a workaround would be to put the standalone root on a set of clustered servers. If one server went down, referrals would continue. The FSMT product team tells me that all parts of FSMT are fully cluster aware and compatible: it will create cluster consolidation DFS roots and add cluster names instead of DNS aliases if roots are hosted on cluster. So â nice touch.
Another problem is that you simply must rename the servers to do any of the redirecting magic. I would love to keep the server, name intact, and just redirect a specific share. This would allow me to keep using the server for whatever else itâs doing, but just migrate the specific shares I want to. To do this, we would need symbolic links within the original share that would route us to the new goal. But right now, Windows Server 2003 isnât quite there. Perhaps with Longhorn server.
The last note here is that youâre not actually forced to turn off servers youâve migrated from. You can, if you so choose, keep the server online performing other roles. The problem is that it might be a challenge having other network services and clients find the newly renamed machine. DFS is some pretty strong magic, but itâs only for files; lots of other services wonât be able to magically find the newly renamed server.
The FSMT is a cool tool, which works as advertised. And the price is rightâfree. It should be noted that as good as the tool is, itâs not meant to be a permanent solution. The help file notes that these consolidated DFS roots shouldnât be maintained forever. The idea is that over time youâll properly design your DFS, point users toward the new, updated structure, and then phase out the roots you created with the DFS Consolidation Wizard.
Hopefully this will get you out of some tough jams, and into your 21st century file servers. Other FSMT resources:
- Newsgroup support
- You can use the microsoft.public.windows.server.migration newsgroup to ask questions about the File Server Migration Toolkit.
- The FSMT Solutions accelerator (additional guidance)
Get signed copies of...
Group Policy, Profiles and IntelliMirror for Windows 2003, Windows XP and Windows 2000 (THIRD EDITION)
-and-
Windows & Linux Integration: Hands on Solutions for a Mixed Environment
Do you have the new THIRD EDITION of the Group Policy book? It's got 50 new pages, fully covers XP/SP2 and Windows Server 2003/SP1, an armload of new tidbits here and there, and whole new section on the Security Configuration Wizard.
Order your signed copy today by clicking here. Additionally available is my new title Windows & Linux Integration: Hands on Solutions for a Mixed Environment fromwww.WinLinAnswers.com/book.
Oh, and if you own either book, and want to say nice things on Amazon, please do so! That would be great. Thanks! You can do so here:
http://www.amazon.com/gp/product/0782144470 (GPO book)
http://www.amazon.com/gp/product/0782144284 (WinLin book)
Choose the right Active Directory and Group Policy Course for you
Did you know that here at GPanswers.com, we have three courses, including an ADVANCED course. (It's true!)
And, historically, I havenât done such a hot job in making it obvious what your available options are for public and private training. So, hereâs the executive summary. Online, we have a new âGroup Policy âRightsizeâ Toolâ which helps you decide the best course to take for your situation.
Two-day intensive Group Policy workshop class
- This course is best for Domain Administrators and qualified OU administrators.
- This course has âintensiveâ in the name, so be prepared to work and learn!
- This class is available as a private two-day course.
- This class is available as a public two-day course.
- Consider adding the One-Day Advanced course (below) as a third-day (if taking as a private two-day)
Three-day âLess Intensiveâ Active Directory warm-up and Group Policy workshop class
- This course starts with a half day warm-up of Active Directory, managing users, and delegating permissions.
- Then, we move on to the Group Policy goodies. This way, those with less Group Policy and day-to-day administration experience can get a bit of the fundamentals before diving into the Group Policy waters.
- This class caters more to OU administrators (than Domain Administrators)
- This "Three-day less-intensive" course is ONLY available as a private course.
- Consider adding the One-Day Advanced course (below) as a fourth day
One-day Group Policy âadvancedâ class
- This class is a great âadd-onâ after your two-day or three-day Group Policy class. We cover four big concepts in this class:
- How to create a âtotally locked downâ workstation
- How to use Group Policy tools to increase your troubleshooting ability
- How to zap registry punches down to your client machines with ADM templates and tools
- How to leverage a test lab for good Group Policy deployment practices
- This class is only available as a private course. Consider adding it to your two-day or three-day private course as an additional day.
- It is suggested (though not required) that students attend either the two-day intensive or three-day less-intensive Group Policy workshop classes before this one.
Upcoming Classes, Appearances and Conferences
Public Two-Day Workshops for the Remainder of 2006:
- Aug 23-24: Denver, CO
- Aug 24â25: Phoenix, AZ
- Sep 25â26 (changed dates): Seattle, WA
- Nov 20-21 (new): Newtown, PA (Close to NY, NJ, PA, DE and more)
Why THESE cities? Because people used the "Suggest a city" form at https://www.gpanswers.com/suggest and ASKED me to have classes here.
Here's hoping you'll take advantage of the opportunity! Learn more and sign up at: https://www.gpanswers.com/workshop
(Don't forget to scroll all the way to the bottom of that page and locate your city!)
Or, if you think you might want your own in-house training (with all the personalized attention that affords), I'd love to join you onsite!
If you have even a handful of in-house people interested in the training, the course pays for itself (as you don't need to ship people offsite!). I'll even travel overseas to the U.K., other parts of Europe, or Japanâor wherever! Have passport, will travel!
Again, while the training course isn't officially endorsed by Microsoft, the class does have the distinction of being a suggested avenue for intense Group Policy training by members of the Group Policy, Microsoft Consulting Services, and Product Support Services teams at Microsoft!
For a public class, sign up online at: https://www.gpanswers.com/workshop/
For a private class, just contact me at [email protected] or call me at 302-351-8408.
Free Education with Moskowitz / Microsoft / Techtarget / Dell Roadshow
Jeremy Moskowitz and TechTarget + Microsoft team up to bring you a 19-city roadshow tour titled: Deployment, Managing, and Monitoring: Getting the Job Done. Here, youâll hear me talk about how to use the tools in the box to deploy your Windows XP, Windows 2003, and Vista systems, how to use Group Policy to manage your systems, and finally how to keep tabs on them with some slick free tools! Did I mention this is 19 cities?? So, thereâs a good chance weâll be near you soon! Check it out and sign up here.
Upcoming Conferences
- TechMentor: Sep 25-29 in Las Vegas. I'll be speaking on Win/Lin integration topics. All sorts of other good stuff. Check it out here. Use promotion code 'moskowitz' when signing up.
- WinConnections: Nov 6-9 in Las Vegas. I'll be doing a pre-con on Group Policy, then some regular sessions on locking down computers, some awesome tips on Group Policy tools, and how to integrate Windows and Linux into Active Directory. Check it outhere.
Welcome New Sponsors
I can't tell you how often I hear that people LOVE the Solutions Guide we have at GPanswers.com/solutions. Inside, you'll find both free and 3rd party products which extend the reach of Group Policy or let you do something you haven't discovered before! Recently we've added:
- NetIQ: Group Policy Administrator
- Smartline: Devicelock
So, head on over to the Solutions Guide and see what other goodies are available!
Subscribe, Unsubscribe, and Usage Information
If you've received this message as a forward from a friend, or are reading it online in the archives, you can sign up for your own newsletter subscription.
Also, if you want to unsubscribe, you can do that, too (but we'll be sad to see you go).
For all Subscription and Unsubscription information, we have a one-stop-shop page at the following address:https://www.gpanswers.com/newsletter
You can use this information as you see fit, but if you're going to copy any portion, please FORWARD THE ENTIRE email.
While Moskowitz, inc. tries to ensure that all information is technically accurate, we make no warranty with regard to the information within. Please use at your own risk.
If you need personalized attention regarding subscriptions and unsubscriptions, just email me: [email protected]
Please POST your technical question on the GPanswers.com/community forum whenever possible.
If you have questions about ordering a book, contact my assistantMark at: [email protected]. I endeavor to respond to everyone who emails.
Thanks for reading!




Comments (0)