GP and MDM Safeguard Holds
While the phrase, “between a rock and a hard place” stems from ancient Greek Mythology, it could easily apply to the task of applying Windows feature updates. A new feature update can integrate new innovation and added value to your users. On the other hand, that same update may also cause an rebellion amongst your helpdesk team as a ticket monsoon is created from that update going bad. It’s a pendulum that can swing both ways.
What are Safeguard Holds?
That’s one reason why Microsoft developed Safeguard holds. Safeguard holds prevent devices with a known compatibility issue from receiving a new feature update. By doing so, it protects users from a potentially poor desktop experience should the updated feature not be a harmonious match for their particular device. Microsoft uses quality and compatibility diagnostic data to identify issues of possible incompatibility. When such a device is identified, it is placed on hold, which serves as a safeguard. Devices that are placed on hold are prevented from installing the designated Windows 10 feature in order to preserve the user experience for the time being. Microsoft then uses the captured diagnostic data to release a fix that addresses the compatibility issue and at some point, the hold will be released. At that point, the update can then be delivered. Microsoft also uses holds when a customer or partner reports a disruptive issue directly related to an update for which an immediate workaround is not available. Those enterprises that utilize Microsoft Endpoint Manager can use Update Compliance reporting retrieve data related to current safeguard holds.
Keep in mind that safeguard holds only apply to Windows devices that use Windows Update for Business. Safeguard holds do not pertain to feature updates that are deployed through other channels such as Windows Server Update Services (WSUS) or installation media. Most enterprises should be using Windows Update for Business as it offers administrators the ability to define Windows Update service rings in order to manage update delivery schedules for different user classifications.
Opting out of Safeguard Holds
Safeguard holds are a good thing. However, there are instances when you might not want them. For instance, internal IT may want to validate the newest feature on a test device (for those who have it, it is best to validate feature updates using the Windows Insider Program for Business Release Preview Channel). Allowing the update to go through will allow you to experience the compatibility issue firsthand as well as assess other implications concerning the update. For those who want to bypass holds for special circumstances, Microsoft released a Disable safeguards for Feature Updates Group Policy late last year. The policy is applicable to any Windows Update for Business device running Windows 10, version 1809 or later with the October 2020 security update installed.
Deploying the Policy
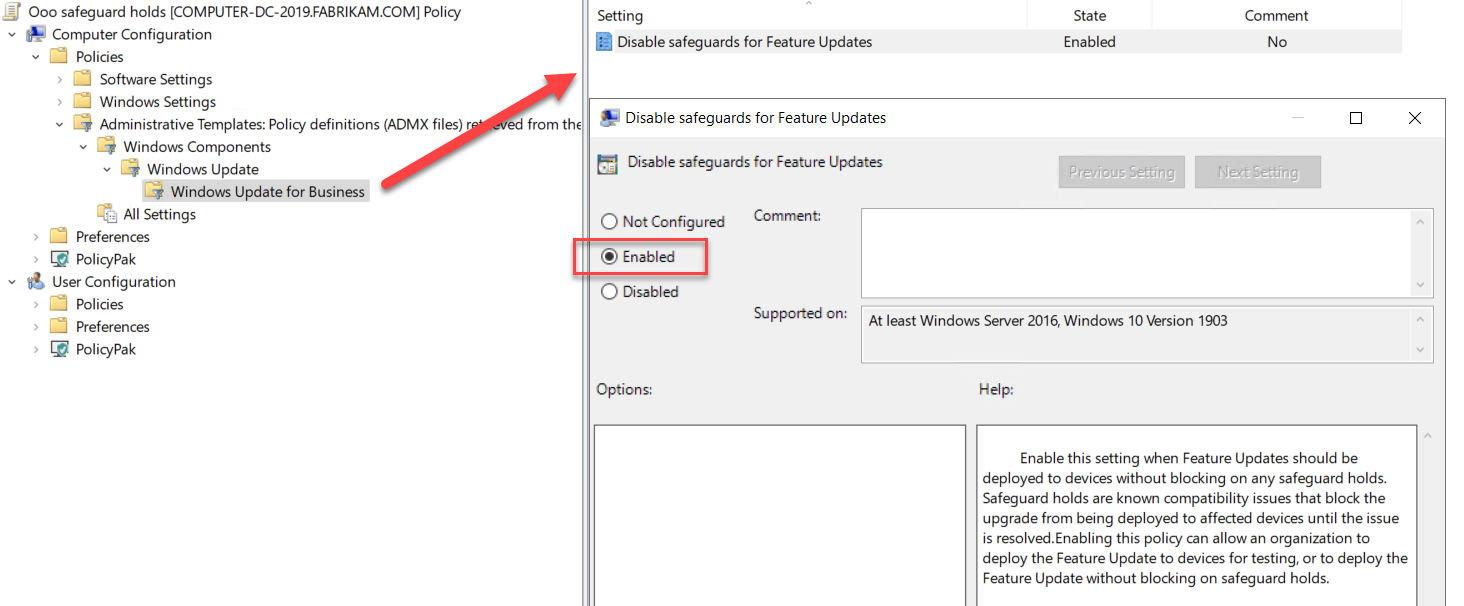
There are several ways to deliver the Disable Safeguards policy to your devices. For domain-joined devices, Group Policy is easy. Create a GPO and go to Computer Configuration > Administrative Templates >Windows Components > Windows Update > Windows Update for Business and enable “Disable safeguards for Feature Updates” as shown in the screenshot below.
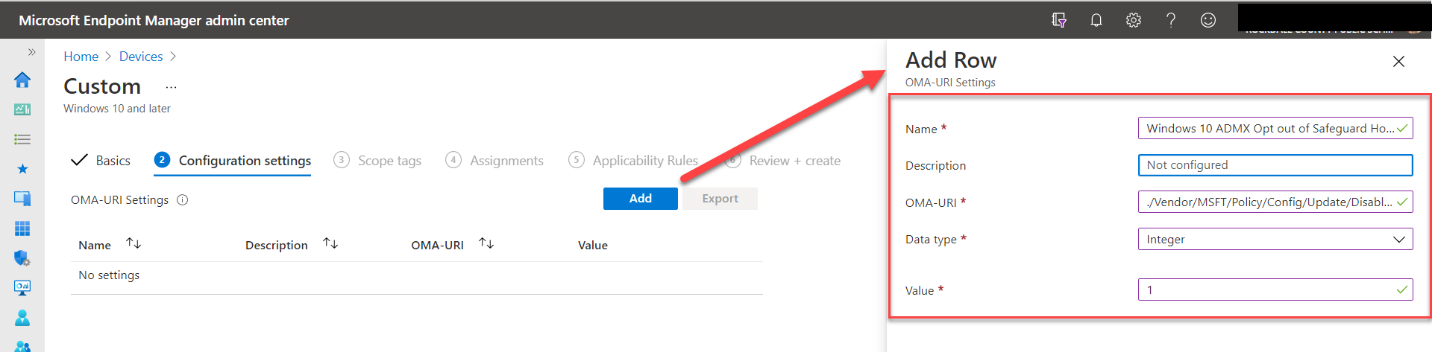
Administrators can also use an MDM such as Microsoft Endpoint Manager to manage your devices, you can create a custom profile to deploy the policy. While the involved settings do not appear in the management interface, you can create a custom device configuration profile using OMA-URI settings. Using Microsoft Endpoint Manager go to Devices and create a custom profile for the Windows 10 platform. Provide a name for the OMA-URI setting and optional description if desired. Then add the following settings as shown in the screenshot below.
- OMA-URI: ./Vendor/MSFT/Policy/Config/Update/DisableWUfBSafeguards
- Data type: Select Integer
- Value: 1
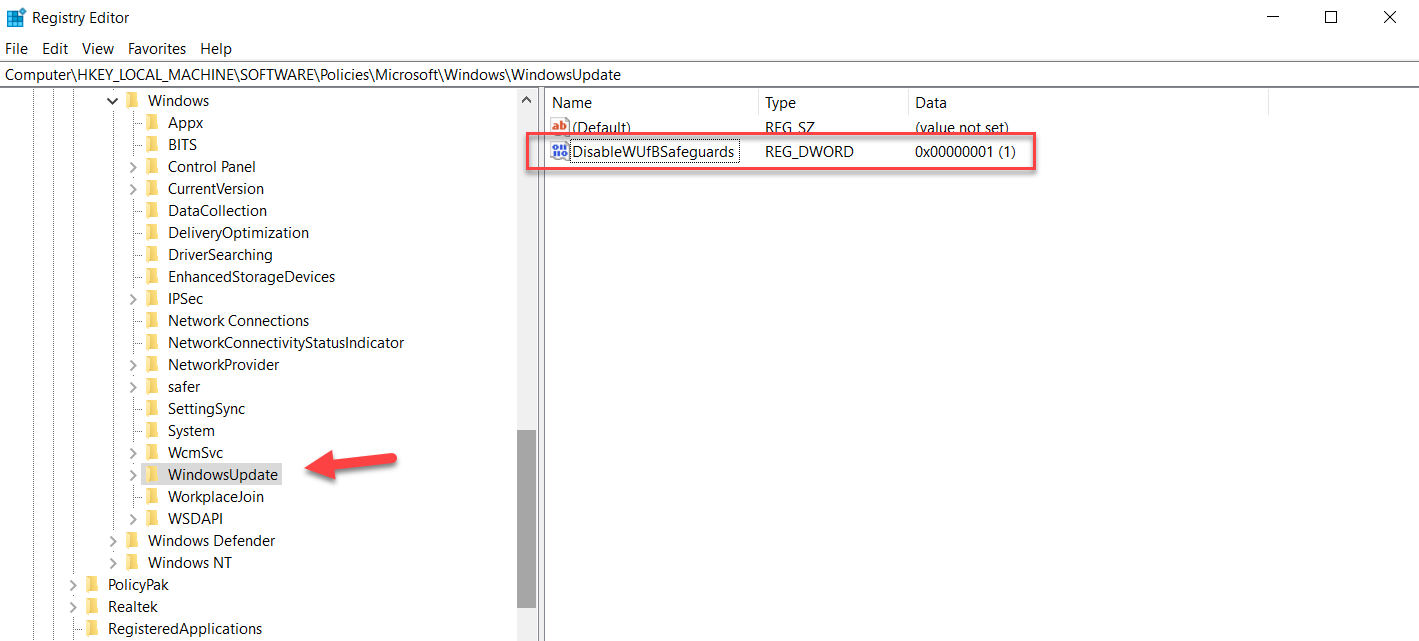
Another way is to modify the registry. You can do this manually or deploy the modification using Group Policy Preferences. Start by going to the following key:
Go to HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate
Right click on WindowsUpdate and select New > Dword (32-bit) Value
Name it DisableWUfBSafeguards
Set its value to “1” and reboot.
The finished result is shown below.
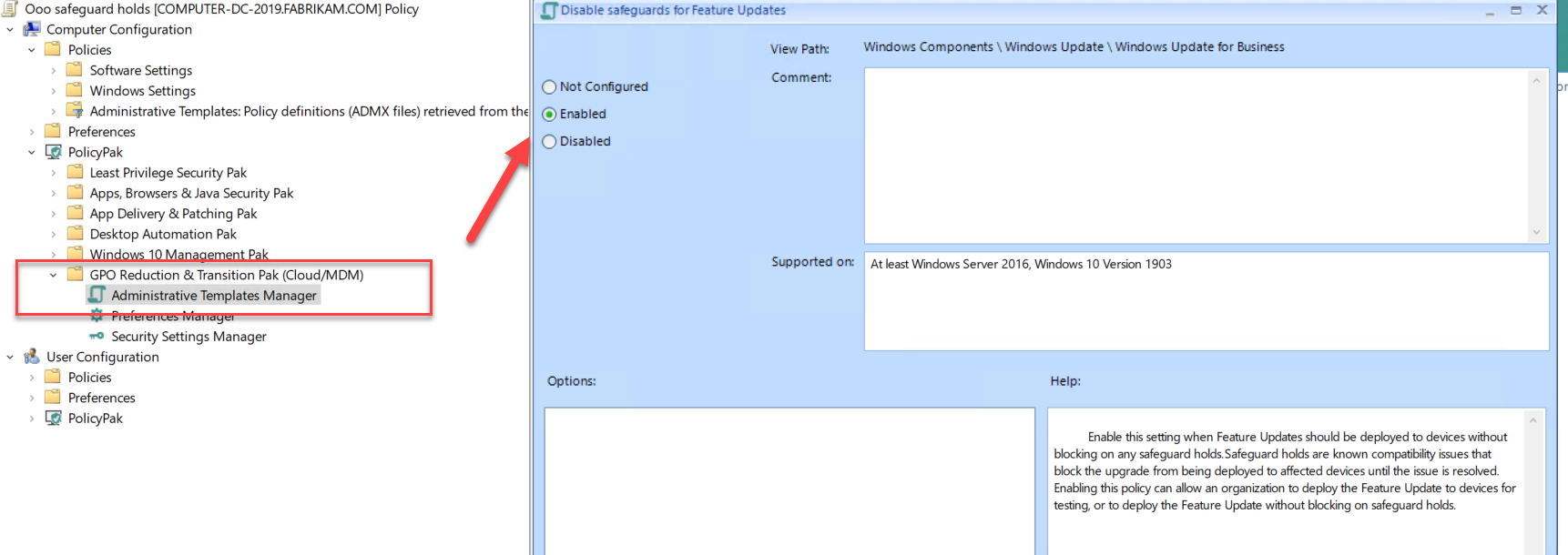
For those enterprises that utilize both domain-joined and non-domain joined machines, there are third party solutions such as PolicyPak that you can use to deploy the Disable Safeguards policy to any internet connected Windows 10 device. In this case, the PolicyPak editors are built inside the Group Policy Management Editor so creating the policy is simple and straightforward. Once created, you can deploy it using standard Group Policy, your chosen MDM solution or PolicyPak Cloud. The screenshot below shows the creation process that utilizes the ADMX templates.
To be clear, you shouldn’t disable Safeguard Holds to rush out feature updates to standard users, but this policy does provide administrators with greater the flexibility they need at times.




Comments (0)