A Further Deep Dive into Windows LAPS (LAPS2)
I am extending my focus on the new Windows LAPS or as I call it, LAPS2. LAPS2 is Microsoft’s newest release of its Local Administrator Solution which fixes some of the shortcomings of its initial release years ago which is now referred to as Legacy LAPS or LAPS1. In Part 1 of this series, we looked at how to implement LAPS2 and configure the new Group Policy settings for it. Today I am going to finish our discussion on implementing LAPS2 in a traditional AD environment.
The New PowerShell Scripts
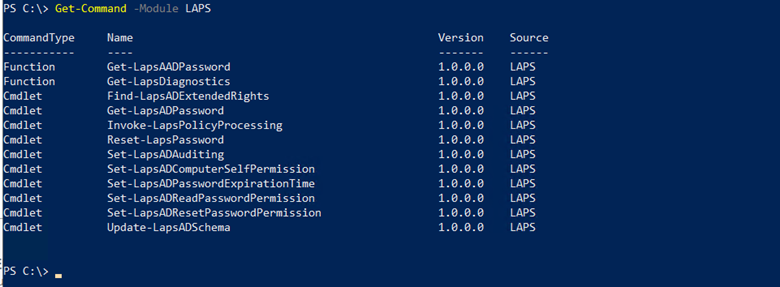
The new LAPS introduces a new set of PowerShell scripts. To get the scripts you will need to add the new PowerShell module using the command: Get-Command -Module LAPS as shown below in the screenshot below.
Here are the scripts that you will find the most relevant:
|
Get-LapsADPassword |
Use it to query Windows Server Active Directory for Windows LAPS passwords. |
|
Get-LapsAADPassword |
Use it to query Azure Active Directory for Windows LAPS passwords. |
|
Reset-LapsPassword |
Use it to initiate an immediate password rotation. |
|
Reset-LapsPassword |
Use it to update a computer’s Windows LAPS password expiration tine in Windows Serve Active Directory |
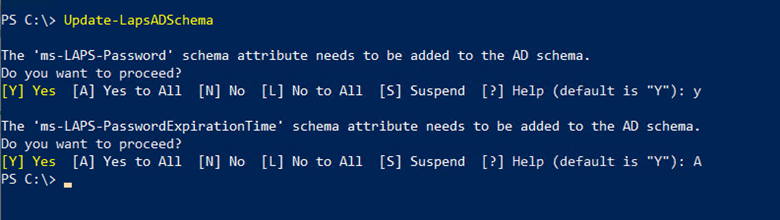
Now let’s put two of these scripts into action. LAPS2 introduces new AD attributes but first you need to update the schema using the Update-LapsADSchema command in PowerShell as shown here.
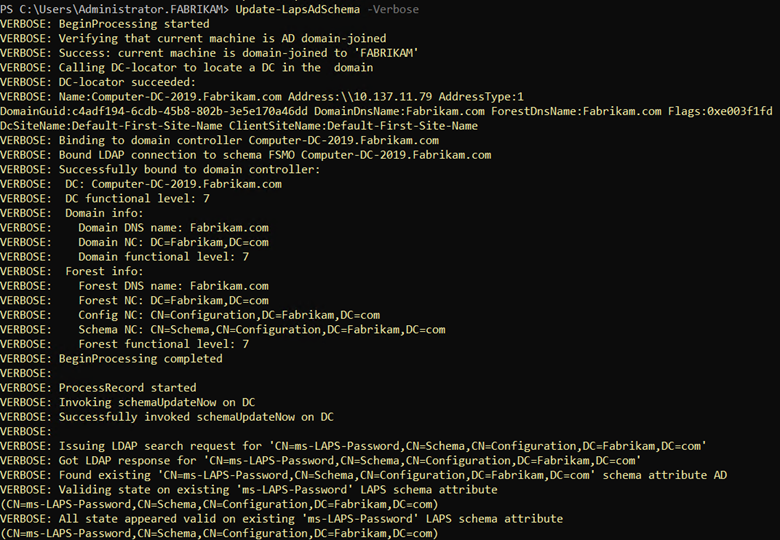
Note that all domain controllers must have the KB5025229 update installed for the command to finish. If the command fails to complete, you can run the Update -LapsADSchema -Verbose command. You can then read the output to either confirm the completion of schema update or find out where the process is erroring out. The screenshot shows a portion of the output which in this case was completed in its entirety.
Next you need to grant permissions to the machines that will be updating their passwords. This is done by setting inheritable permission to the Organizational Unit(s) where the target machines reside using the Set-LapsADComputerSelfPermission command. In the example below I assigned the permission to the Servers OU.
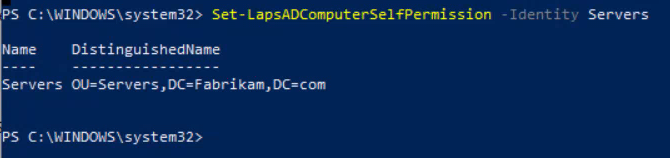
If you don’t see the Distinguished Name in the output, then the command did not complete.
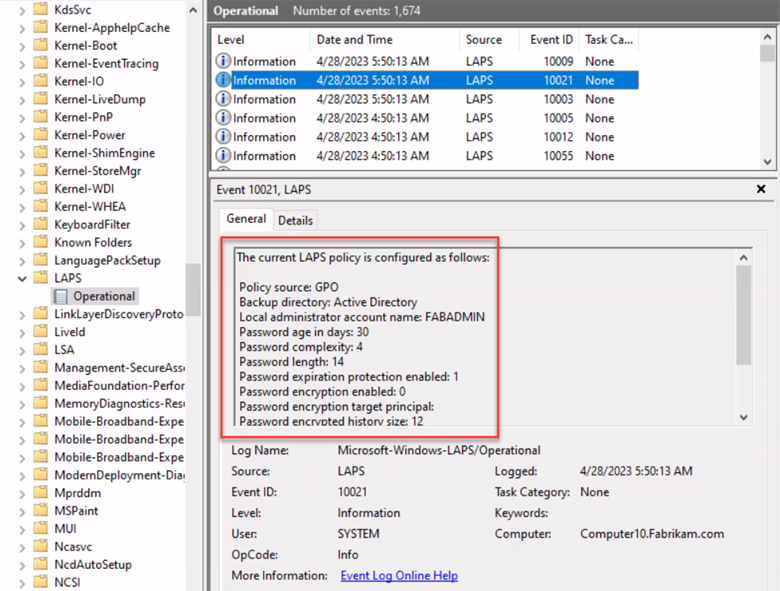
Once the PowerShell commands have been run, deploy your LAPS GPO and you should be good to go. You can confirm the GPO settings were implemented by going to Event Viewer and confirming it in your LAPS file. You can navigate there by going to:
Application and Service Logs > Microsoft > Windows > LAPS > Operational.
The screenshot below shows that the LAPS policy has been successfully configured.
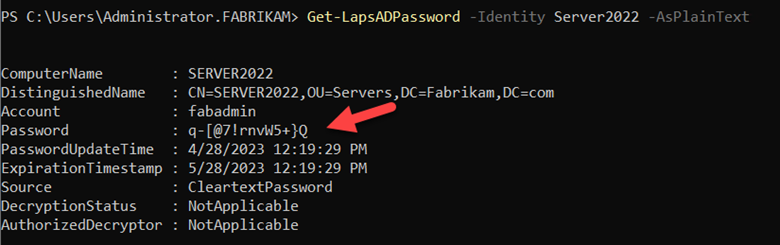
Now that the LAPS policy is implemented, its time to retrieve the passwords to login to the machines. There are two ways to do this. You can use the following command in PowerShell:
Get-LapADPassword -Identity Server2022 -AsPlainText as shown below.
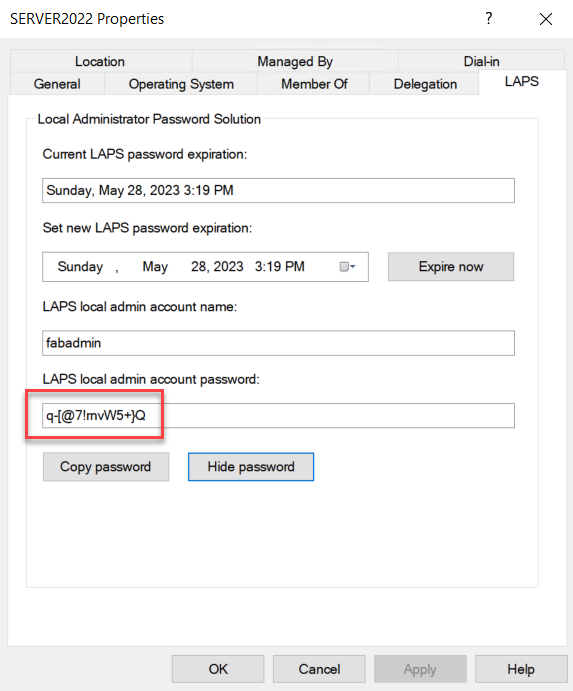
You can also use Active Directory. Remember we updated the schema which created new AD attributes. Find the designated computer in Active Directory Users & Computers and view its properties. Then click on the LAPS tab to view the LAPS settings as shown below.
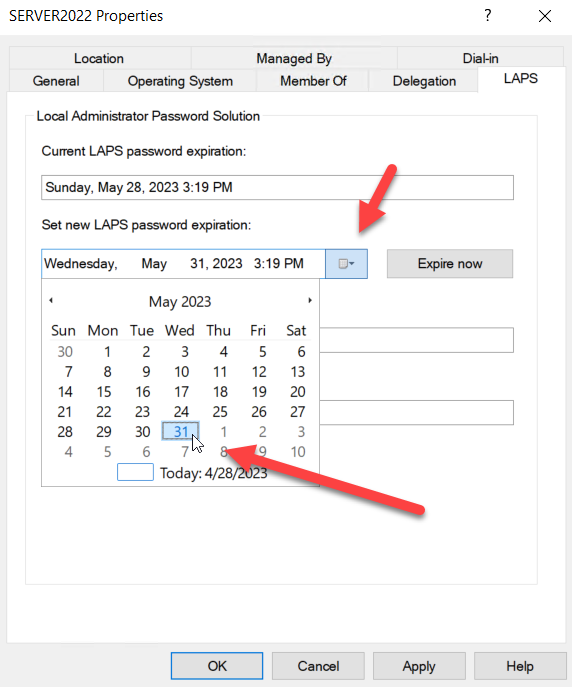
Note that you can also modify the expiration date for the LAPS generated password using this tab as shown here.
If you are having trouble getting LAPS to work properly here are two possible gotchas:
- Your LAPS password policy must be in line with your domain password policy. In other words, you cannot configure an 8-character password for LAPS if your domain requires a 10 character and you must enforce the same complexity requirements or greater.
- Be sure to reboot the computers that you are assigning the LAPS policy to.
Emulation Mode
If a machine has already been using the original LAPS (LAPS1) then the new features of LAPS2 will not be available to it. Running both versions within your environment is referred to as LAPS Emulation Mode. If a LAPS2 policy is present on the machine, it will always take precedence, regardless of how it was applied. In other words, once a LAPS version is applied to a machine, the other one will not work. In our next installment I will discuss how to uninstall LAPS1 from your environment and escape this complexity.




Comments (0)